Problem
When you create a user account for a Windows service to run as, usually default setting is applied to that account. That is, the account can be used for interactive login.
Solution
After I came across two articles here and here, I worked out my own way for doing this on Windows Server 2008 SP2.
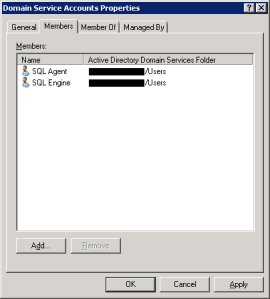
- On the domain controller, create a Global Security group named Domain Service Accounts (optionally with description All domain service accounts)

- Add the service accounts that you want to deny interactive login to the new created group Domain Service Accounts
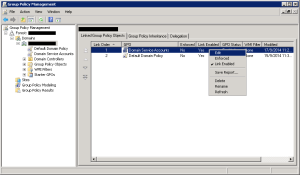
- Run Group Policy Management, on the left navigation pane, expand Group Policy Management > Forest > Domains and right click on the domain name you would like to apply the deny login and select Create a GPO in this domain, and Link it here… from the menu
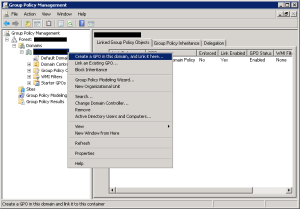
- Give the new GPO a name called Domain Service Accounts and click OK
- On the left navigation pane, under the domain name, expand Group Policy Objects, click on the GPO Domain Service Accounts and set the GPO Status to User configuration settings disabled as user configuration settings will not be used
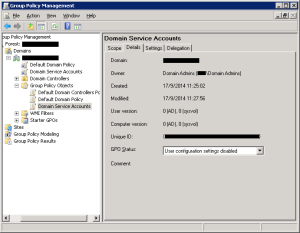
- On the left navigation pane, click on the domain name, and on the right pane, in the Linked Group Policy Objects tab, reorder the GPO Domain Service Accounts to have link order smaller than the Default Domain Policy, then right click on the GPO Domain Service Accounts and select Edit from the menu
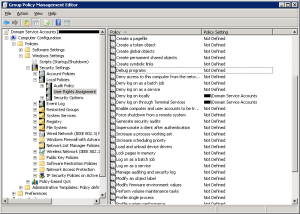
- On the new popped up Group Policy Management Editor, on the left navigation pane, expand Domain Service Accounts > Computer Configuration > Policies > Windows Settings > Security Settings > Local Policies > User Rights Assignment, add the group Domain Service Accounts in the two policy Deny log on locally and Deny log on through Terminal Services